Azure AD®
You can integrate Microsoft Azure AD® (Active Directory) with Cloudflare Zero Trust and build policies based on user identity and group membership. Users will authenticate to Zero Trust using their Azure AD credentials.
The following Azure AD values are required to set up the integration:
- Application (client) ID
- Directory (tenant) ID
- Client secret
To retrieve those values:
-
Log in to the Azure dashboard.
-
Go to All services > Azure Active Directory.
-
In the Azure Active Directory menu, go to Enterprise applications.
-
Select New application > Create your own application.
-
Name your application.
-
Select Register an application to integrate with Azure AD (App you’re developing) and then select Create.
-
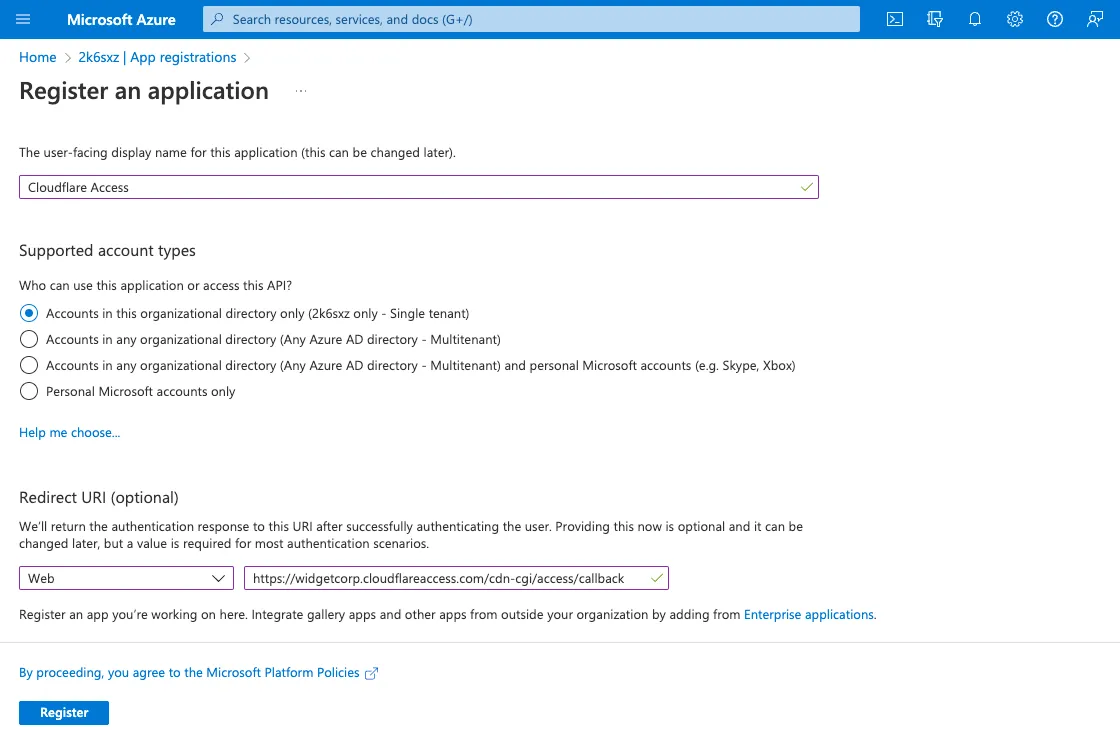
Under Redirect URI, select the Web platform and enter the following URL:
https://<your-team-name>.cloudflareaccess.com/cdn-cgi/access/callbackYou can find your team name in Zero Trust under Settings > Custom Pages.
-
Select Register.
-
Next, return to the Azure Active Directory menu and go to App registrations.
-
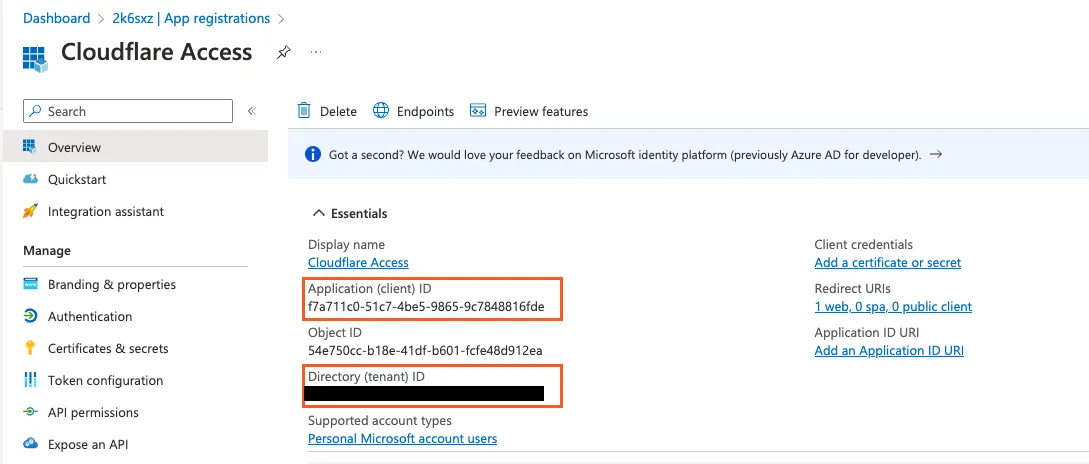
Select the app you just created. Copy the Application (client) ID and Directory (tenant) ID.
-
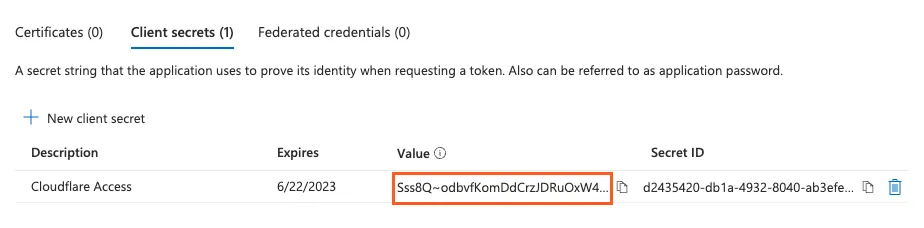
Go to Certificates & secrets and select New client secret.
-
Name the client secret and choose an expiration period.
-
After the client secret is created, copy its Value field. Store the client secret in a safe place, as it can only be viewed immediately after creation.
-
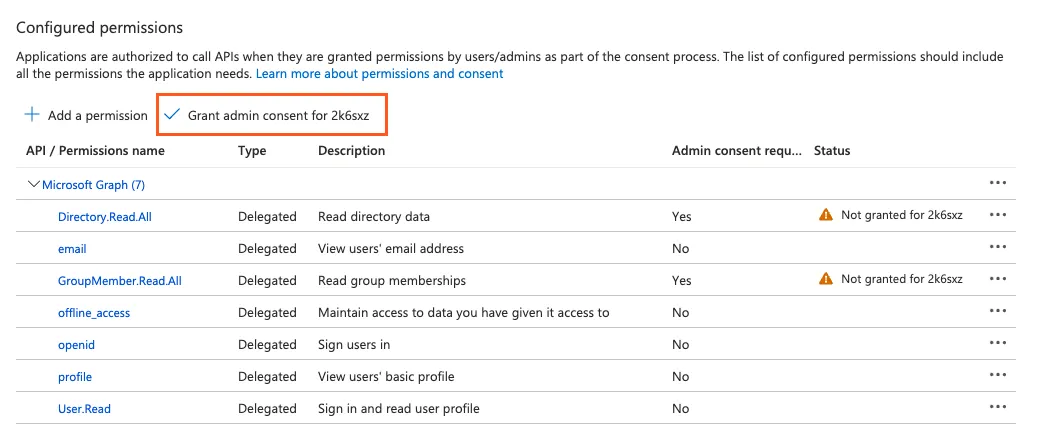
From the App registrations page for your application, go to API permissions.
-
Select Add a permission.
-
Select Microsoft Graph.
-
Select Delegated permissions and enable the following permissions:
emailoffline_accessopenidprofileUser.ReadDirectory.Read.AllGroupMember.Read.All
-
Once all seven permissions are enabled, select Add permissions.
-
Select Grant admin consent.
-
In Zero Trust, go to Settings > Authentication.
-
Under Login methods, select Add new.
-
Select Azure AD.
-
Enter the Application (client) ID, Client secret, and Directory (tenant) ID obtained from the Azure dashboard.
-
(Optional) Configure the following settings:
- Proof Key for Code Exchange: Perform PKCE on all login attempts.
- Support Groups: Allow Cloudflare to read a user’s Azure AD group membership.
- Azure AD Policy Sync: Refer to our Azure AD Conditional Access tutorial.
- Enable SCIM: Refer to Synchronize users and groups.
- Email claim: Enter the Azure AD claim that you wish to use for user identification (for example,
preferred_username). - OIDC Claims: Enter custom OIDC claims that you wish to add to your users’ identity. This information will be available in the user identity endpoint.
-
Select Save.
To test that your connection is working, select Test.
The Azure AD integration allows you to synchronize IdP groups and automatically deprovision users using SCIM.
- Microsoft Entra ID P1 or P2 license
-
In Zero Trust, go to Settings > Authentication.
-
Locate the IdP you want to synchronize and select Edit.
-
Select Enable SCIM and Support groups.
-
(Optional) Enable the following settings:
- Enable user deprovisioning: Revoke a user’s active session when they are removed from the SCIM application in the IdP. This will invalidate all active Access sessions and prompt for reauthentication for any Gateway WARP session policies.
- Remove user seat on deprovision: Remove a user’s seat from your Zero Trust account when they are removed from the SCIM application in the IdP.
- Enable group membership change reauthentication: Revoke a user’s active session when their group membership changes in the IdP. This will invalidate all active Access sessions and prompt for reauthentication for any Gateway WARP session policies. Access will read the user’s updated group membership when they reauthenticate.
-
Select Save.
-
Copy the SCIM Endpoint and SCIM Secret. You will need to enter these values into the IdP.
The SCIM secret never expires, but you can manually regenerate the secret at any time.
-
In the Azure Active Directory menu, go to Enterprise applications.
-
Select New application > Create your own application.
-
Name your application (for example,
Cloudflare Access SCIM). -
Select Integrate any other application you don’t find in the gallery (Non-gallery).
-
Once the SCIM application is created, assign users and groups to the application.
-
Go to Provisioning and select Get started.
-
For Provisioning Mode, choose Automatic.
-
In the Tenant URL field, enter the SCIM Endpoint obtained from Zero Trust.
-
In the Secret Token field, enter the SCIM Secret obtained from Zero Trust.
-
Select Test Connection to ensure that the credentials were entered correctly.
-
Select Save.
-
On the Provisioning page, select Start provisioning. You will see the synchronization status in Azure.
To check which users and groups were synchronized, select View provisioning logs.
Provisioning attributes define the user properties that Azure AD will synchronize with Cloudflare Access. To modify your provisioning attributes, go to the Provisioning page in Azure AD and select Edit attribute mappings.
We recommend enabling the following user attribute mappings:
| customappsso Attribute | Azure AD Attribute | Recommendation |
|---|---|---|
emails[type eq "work"].value | mail | Required |
name.givenName | givenName | Recommended |
name.familyName | surname | Recommended |
When SCIM synchronization is enabled, your Azure group names will automatically appear in the Access and Gateway policy builders.
If building an Access policy, choose the Azure Groups selector.
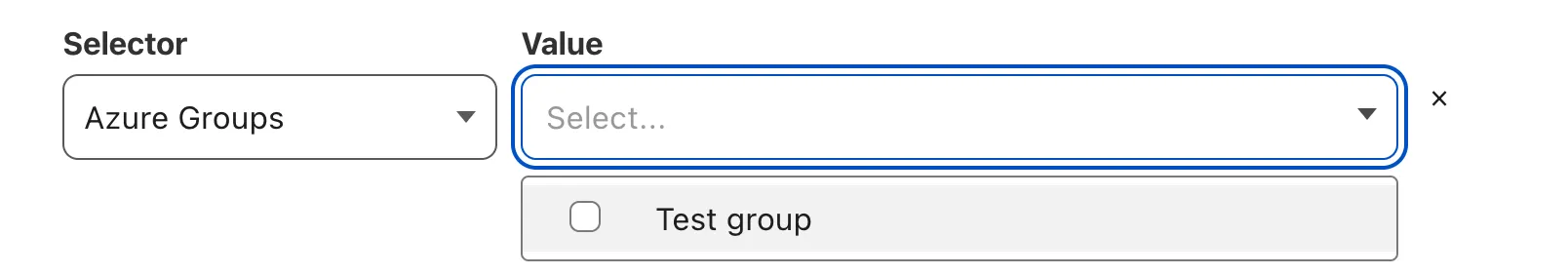
If building a Gateway policy, choose the User Group Names selector.
You can create Access and Gateway policies for groups that are not synchronized with SCIM. Azure AD exposes directory groups in a format that consists of random strings, the Object Id, that is distinct from the Name.
-
Make sure you enable Support groups as you set up Azure AD in Zero Trust.
-
On your Azure dashboard, note the
Object Idfor the Azure group. In the example below, the group named Admins has an ID of61503835-b6fe-4630-af88-de551dd59a2.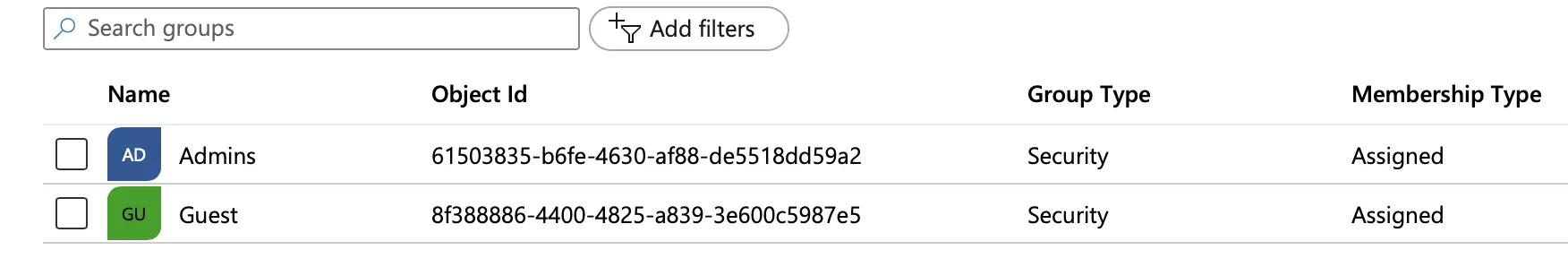
-
If building an Access policy, choose the Azure Groups selector. If building a Gateway policy, choose the User Group IDs selector.
-
In the Value field, enter the
Object Idfor the Azure group.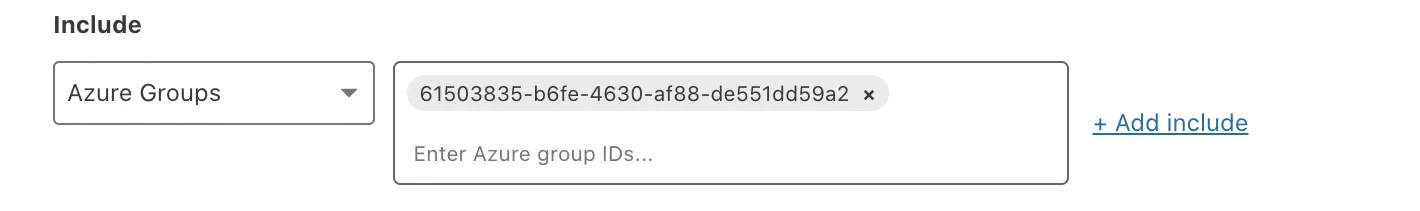
Access and Gateway policies for an Azure group will also apply to all nested groups. For example, if a user belongs to the group US devs, and US devs is part of the broader group Devs, the user would be allowed or blocked by all policies created for Devs.
You can require users to re-enter their credentials into Azure AD whenever they re-authenticate their WARP session. To configure this setting, make a PUT request and set the prompt parameter to either login or select_account.
{ "config": { "client_id": "<your client id>", "client_secret": "<your client secret>", "directory_id": "<your azure directory uuid>", "support_groups": true }, "type": "azureAD", "name": "my example idp"}